This report will consist of publicly available information and information gathered with Freedom of Information Act request, it will be chronologically structured and is not intended to change your opinion of our country, but only seeks to remind you of the constitutional foundations in which this country was ordained.
This is Orwellianism…welcome!
1960-2001
ECHELON was created in the 1960’s to help monitor the Soviet Union and Eastern Bloc allies during the cold war. Echelon was officially established in 1971, but it didn’t stay secret for long just one year later in 1972 commentary from a man named Winslow Peck came to light on Rampart’s, in which he revealed that the NSA had a global network of listening post, Winslow Peck was not his real name, his real name was Perry Fellwock and he was a former NSA analyst. Mr. Fellwock’s commentary on Ramparts is one of the first mentions ever of the NSA’s top-secret program code-named ECHELON.
It would be ten years before the next far more public revelations of ECHELON were revealed in James Bamford’s 1982 book The Puzzle Palace. In his book, James Bamford describes ECHELON as the software controlling the collection and distribution of civilian telecommunications traffic conveyed using communication satellites, with the collection being undertaken by ground stations located in the footprint of the downlink leg.
A woman by the name of Margaret Newsham who was employed at Lockheed Martin, from 1974-1984 in Sunnyvale, California and Menwith Hill in England told a member of Congress in 1988 that ECHELON was used to collect the phone calls of Republican Senator Storm Thurmond, she stated “that targeting of U.S. political figures would not occur by accident, but was designed into the system from the start.”
She went on to explain how ECHELON is the code name for the NSA’s computer program, Lockheed called it P415 and the software programs were called SILKWORTH and SIRE. Newsham revealed the satellite for ECHELON was called VORTEX which intercepts communications around the world using a global network of listening-post. Douglas Campbell also wrote an article in 1988 entitled “Somebody’s Listening” for the New Statesman in which he wrote about the signal intelligence gathering activities of a program code-named ECHELON.
1996 was dominated by the revelations made in Nicky Hager’s book entitled “Secret Power” in which he went into great detail about what we now know as Five Eyes and Australia’s role in the international spy network. Secret Power was the basis for an investigation into this spy network by the European Parliment in 2001.
On February 25th, 1996 the National Reconnaissance Office was declassified in this declassification we found out the NRO had been in operation since 1959 with it’s Corona Satellite later they would add Argon and Laynard, but these satellites were used to spy on our enemies and to protect us against a very real threat from the USSR much like many of these early programs they had a real purpose against a specific threat compared to surveillance programs today that vacuum up mass amounts of data and write algorithms to make sense of the data they are accumulating when in fact, all it does is make it harder for government to protect our national security.
James Woosley former director of the CIA confirmed the existence of ECHELON in 2001, he explained that U.S. intelligence uses interception systems and keyword searches to monitor “European businesses”, but the New York Times reported the contrary penning avid fears that the ECHELON program could be used to spy on U.S. citizens saying the ECHELON program “emerged from the Cold War as a Big Brother without a cause.”
2001- Present
In October 2001 President Bush signed an executive order called the President’s Surveillance Program it was known as “the program”. This program is publically known today as Steller Wind and because of Edward Snowden and Thomas Drake, we now know that Stellar Wind involved the government having secret deals with the big telecommunication companies like AT&T and Verizon who still have deals today with the government that stampede all over our fourth amendment right against illegal search and seizures.
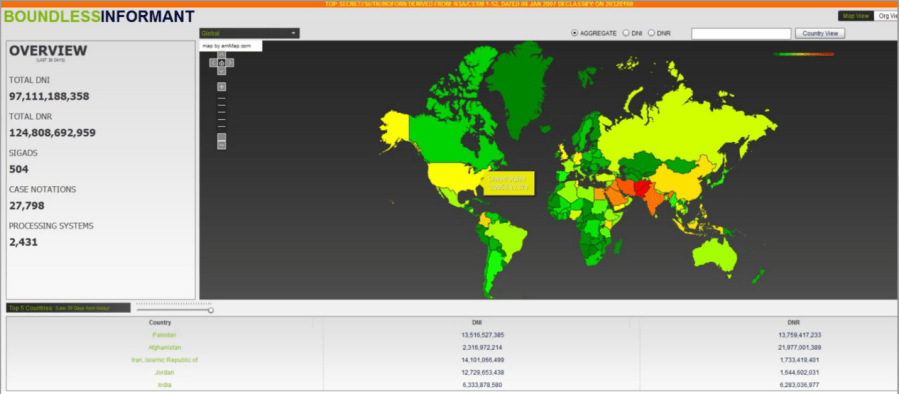
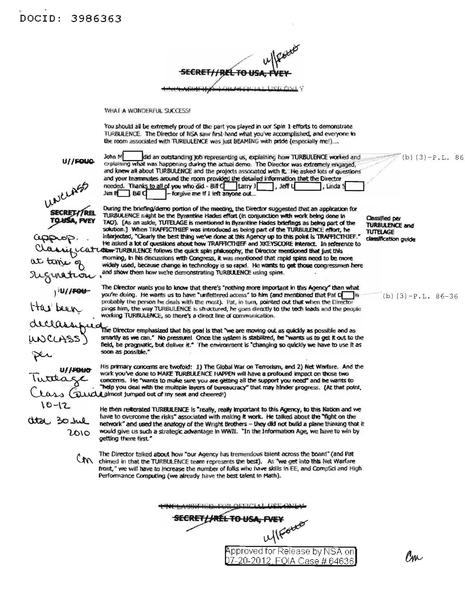
Stellar Wind then morphed into Trailblazer as the NSA had trouble keeping up with the explosion of the digital age so they initiated the “take it all” strategy. After the NSA had been collecting this data for years they failed to make sense out of any of it, Trailblazer was a failure and didn’t successfully stop a single terrorist attack or have even one arrest accredited the vast amounts data it vacuumed up. Thomas Drake said it the best “instead of looking for the needle in the haystack, they created more haystacks” now the NSA needed to make sense of the terabytes upon terabytes of data they were accumulating in order to justify the growing budget of the mass surveillance programs. The NSA’s answer to this was and still is to this day a program called Turbulence.
These programs spider web off into many other programs, below, we will explain what they do and how they are integrated into one massive global surveillance program, we will also detail government contractors and what has grown to be a gigantic multi-billion dollar industry built on the foundation of violating not only our rights as Americans but the rights of citizens around the world. After the Snowden leaks, I was discouraged to see the vast amounts of people who outright didn’t care as if the protection against illegal search and seizure was nothing but words on a piece of paper and not one of the foundations of this Constitutional Republic. Mass surveillance puts us in danger and does not protect us, this is evident in the Boston Bombing case, the San Bernardino case and countless others including the 9/11 terrorist attacks, but how long will we allow for our rights violated under the illusion that it is for our safety?
In my humble opinion, it is not about safety or national security at all it’s not about justice or peace, it’s about power. As former Director of the NSA Michael Hayden told NSA whistleblower Thomas Drake when Drake questioned Hayden on the constitutionality of the mass surveillance program to which Hayden replied: “We have the power.”
In October of 2001, the NSA had awarded 55 contracts to only 144 contractors by October of 2003 the number of contracts had grown to 7.197 given to 4,388 contractors. The United States took a robust highly effective Cold War defense mechanism and turned it into a modern-day Orwellian overseer of all. People often say the government uses metadata to kill people, but they don’t, the government ask someone else to take another humans life based on metadata, it’s reminiscent of Odin from Greek Mythology sending his hawks to do his dirty work.
Mass data mining of our personal private information in the form of data is unconstitutional by all means, but taking another life using data is a failure of our own morality as a civilized society. After spending obscene amounts of taxpayer dollars to build these programs they decided to lease these extraordinary unconstitutional eavesdropping abilities to private entities known as “government contractors” who profit billions of dollars and have absolutely no oversight.

Government Contractors
Battelle Memorial Institute – was officially established in 1929 in Columbus, Ohio although the number of employees they had exploded from 500 to over 20,000, the explosion in employees was due to Battelle Memorial Institute becoming a government contractor in the early 1990’s, they also have 100 international locations. Battelle is at the top of this list because they claim to be a charitable organization that pays zero in taxes on their 10 billion dollars in annual revenue. Battelle’s has 16 government clients and they serve some of the world largest corporations as well as over 800 federal, state and local government agencies. Thier services include border control, counterintelligence, disaster preparedness, ground force operations, human intelligence, intelligence analysis, law enforcement, air, and satellite operations.
Honeywell, Inc – is headquartered in Morristown, New Jersey and it is known as a $34b dollar diversified technology and manufacturing global leader. Honeywell has 95 national and international locations with over 115,000 employees. Honeywell’s actual annual revenue is believed to be much higher at over 50 billion and they have 9 government clients in which they offer “support” for cyber operations, satellite operations, weapons technology, human intelligence, information technology and technical intelligence.
Six3 Systems, Inc – is located in Mclean, Virginia and they have 20 unknown locations with over 500 employees. Six3 Systems revenue is not publically available, but they have 17 government contracts that assist the government in air operations, satellite operations, ground force operations, law enforcement, human intelligence and intelligence analysis they also are involved in counter-IED explosives, building, and personal security.
21st Century Systems, Inc – was established in 1996 in Omaha, Nebraska as well as two top-secret locations, they have up to 500 employees, 21st Century Systems is a 100 million dollar a year company that has 5 government clients who provide support with air and satellite, cyber operations, information technology, intelligence analysis, nuclear operation and psychological operations.
Oracle – was established in 1977 and is headquartered in Redwood, California, it is a publically held company with 5 additional top-secret locations, it is the worlds largest enterprise software company with 10,000 plus employees and an annual revenue of up to 50 billion. Oracle is a publicly held company that has 16 government clients who assist the government with border control, counterintelligence, disaster preparedness, law enforcement, information technology. human intelligence, psychological operations, intelligence analysis, technical analysis, building and personal security.
Scitor Corporation – is located in Herndon, Virginia it was established in 1979, it has over 2000 employees and has an annual revenue of 750 million dollars. Scitor Incorporated has 17 government clients and assists the government in management consulting and administration, air and satellite operations, border control, disaster preparedness, ground force operations, intelligence analysis, law enforcement, nuclear operations and technical intelligence. According to Scitor’s website, it says their staff includes scientist, analyst, former military, intelligence officials, engineers and mathematicians, the majority of their staff has Top-secret and Sensitive Compartmented Information (SCI) clearances.
Intelligent Software Solutions, Inc – prides itself on being one of the country’s fastest-growing software companies it was founded in 1997, it has offices in Colorado Springs, Colorado, Hampton, Virginia, Washington D.C. and Rome, New York, and unknown locations. ISS has a annual revenue of a little less than 100 million and it has over 500 employees. ISS maintains 17 government clients that assist the government in air and satellite operations, counterintelligence, intelligence analyst, naval operations and technical intelligence
Chenega – was established in 1974 and it is located in Anchorage, Alaska it is privately held and has up to 10,000 employees, Chenega has 29 unknown top-secret locations and it has 17 active government contracts in which it assists the government in management consulting and administration, air and satellite operations, border control, counterintelligence, ground force operations, weapons technology, human intelligence, law enforcement, naval operations, staffing and personnel, building and personal security, specialized military operations, technical intelligence and training.
MITRE – is headquartered in Bedford, Massachusetts (for my Wastelanders its the Institute) it is a not-for-profit organization that claims to work in the public interest as a “National Resource” their website states “We apply our expertise in systems engineering, information technology, operational concepts, and enterprise modernization to address our sponsors critical needs.” MITRE manages four Federally Funded Research and Development Centers (FFRDCs), the Department of Defense’s Command Control, Communications Intelligence, the Federal Aviation Administration’s Center for Advanced Aviation System Development, the Veterans Affairs and Internal Revenue Service’s Center for Enterprise Modernization and the Department of Homeland Security’s Systems Engineering and Development Institute.
MITRE has its own independent research and development program that according to their website “explores new technologies and new uses of technologies to solve our sponsor’s problems in the near term and the future.” MITRE has over 7,000 scientist, engineers and support specialist with an astounding 65% of them having their Masters or their Ph.D. MITRE is not on this list because I think they some kind of spy organization that violates our rights every day, but because if MITRE claims to serve the public interest than open it’s doors to public, declassify your research projects and explain to the American people not just our government what it is exactly that you do? MITRE has 16 government clients with an annual revenue of 10 billion. MITRE worked on a program before 9/11 called P-tech, it is my opinion which is backed by other researchers findings that P-tech facilitated one of the greatest heists in history during one of the grandest false-flags in history 9/11.
Stanley – is headquartered in Arlington, Virginia, it has over 5000 employees at over 100 locations. Stanley was founded in 1968 and it publicly trades on the NYSE under SXT, it has an annual revenue of over 10 billion dollars. Stanley stuck out to me because of their heinous “cyber operations” thus I figured it was justifiable to expose their hierarchy, DuckDuckgo their names intriguing what you will find :
Phil Nolan Chairman, President & CEO, George Wilson, Stanley Executive Vice President, Bill Karlson, Director, James C. Hughes, Outside Director, Lieutenant General Richard L. Kelly, USMC (Ret.), Outside Director, Charles S. Ream; Outside Director, John P. Riceman; Outside Director, General Jimmy D. Ross, USA (Ret.); Outside Director
Stanley has been busy in recent years buying up smaller government contractors and expanding their capabilities, they bought Lawton an Oklahoma Techrizon also Oberon Associates Inc which specialized in biometrics. What worst is Stanley is evil on both sides of the invasive data mining free for all by working huge corporations and the government. Stanley has 12 government clients that assist the government in air and satellite, border control, counterintelligence, cyber operations, ground force operations, human intelligence, law enforcement, naval operations and technical intelligence.
Some people are aware of the Orwellian States we all live in, but not everyone is, it is up to us to enlighten the public of how government spying and invasive data mining by huge companies is a violation of not only our privacy but our sovereignty. Our data is our property and once people realize that, it will change the dynamics of data mining forever. We are the civilians of their civility and its time we let our voices be heard. People like Julian Assange and Edward Snowden gave up all they held dear and like so many other truthtellers they put themselves on the altar of liberty for the sake of an informed public and they would do it again in the blink of an eye, to Thomas Drake, Edward Snowden, and Julian Assange I am indebted a lot, but most of all it is my own cognitive awakening.

By Joziah – @dapeaple 4/2/18
